There’s a distinct feeling of deja vu. Just when some Russians were heaving a sigh of relief that this time, unlike four years ago, Russia was not accused of meddling in the U.S. presidential election, news came of a massive hack of several U.S. government agencies. Again, accusing fingers were almost immediately pointed at Russia. Some called it an invasion; others compared it to Pearl Harbor. Senior politicians demanded retribution.
Yet the present case is different to 2016. Essentially, the hacking was aimed at collecting information, rather than manipulating the target country or causing physical damage. Spying is, of course, one of the world’s oldest professions, and has been universally considered an inalienable part of statecraft. Everyone does it. Of all nations, the United States is perhaps best equipped for it, and is likely most active. Edward Snowden and Wikileaks have supplied mountains of evidence to support that.
Attribution of cyberattacks is notoriously tricky. Yet the Americans are certain that the origin of the current massive hack in the United States is the Russian Foreign Intelligence Service (SVR), which celebrated its centenary last Sunday. If—despite the official Kremlin denial—that is the case, it is indeed a major achievement for Moscow, and an indicator of its cyber power. But it comes with strings attached.
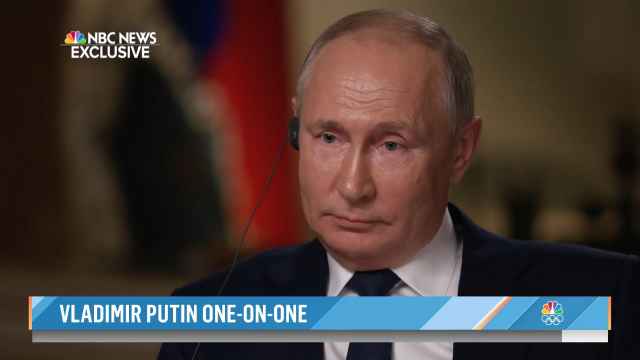
Tit-for-tat is an established modus operandi among hostile intelligence services. What is not clear is what kind of retaliation the United States will eventually decide upon. President-elect Joe Biden will probably be in charge by the time the U.S. response is launched, and it might go beyond sanctions. How far beyond? Ron Klain, the incoming White House Chief of Staff, has suggested that it could well be a cyberattack, going beyond a “mirroring” hacking operation.
Therein lies the problem. In the hybrid war now being fought between America and Russia, the information domain is a principal battlefield, and cyber tools are the weapons of first resort. Yet unlike in the nuclear sphere, there are no rules governing the increasingly intense rivalry.
The line between cyber espionage and cyber warfare is rather blurred. Latter-day Trojan horses can do much more than furnishing critical intelligence: like their ancient model, they can disable the adversary’s defenses or even manipulate the enemy to their advantage. It’s true that something of that kind was always possible: remember the World War II-era radio games. Yet now the scope, scale, and impact of such operations is incomparably greater.
Cyber intelligence, however intrusive, is one thing. Cyber war is another. A kinetic state-versus-state collision, traditionally known as a shooting war, is yet another category. Yet Democratic Senator Richard Durbin has already called the operation attributed to SVR an act of war. The United States policy does allow for the use of military force in response to hostile actions short of war, as is commonly understood. Of course, the decision will rest with the U.S. president.
This article was first published by the Carnegie Moscow Center.
A Message from The Moscow Times:
Dear readers,
We are facing unprecedented challenges. Russia's Prosecutor General's Office has designated The Moscow Times as an "undesirable" organization, criminalizing our work and putting our staff at risk of prosecution. This follows our earlier unjust labeling as a "foreign agent."
These actions are direct attempts to silence independent journalism in Russia. The authorities claim our work "discredits the decisions of the Russian leadership." We see things differently: we strive to provide accurate, unbiased reporting on Russia.
We, the journalists of The Moscow Times, refuse to be silenced. But to continue our work, we need your help.
Your support, no matter how small, makes a world of difference. If you can, please support us monthly starting from just $2. It's quick to set up, and every contribution makes a significant impact.
By supporting The Moscow Times, you're defending open, independent journalism in the face of repression. Thank you for standing with us.
Remind me later.